Sample Software Bill of Materials (SBOM)
Download now
Executive Summary
The monumental increase in recent software supply chain attacks has prompted the US federal government and enterprises globally to require SBOMs as a standard business practice.
What's in an SBOM?
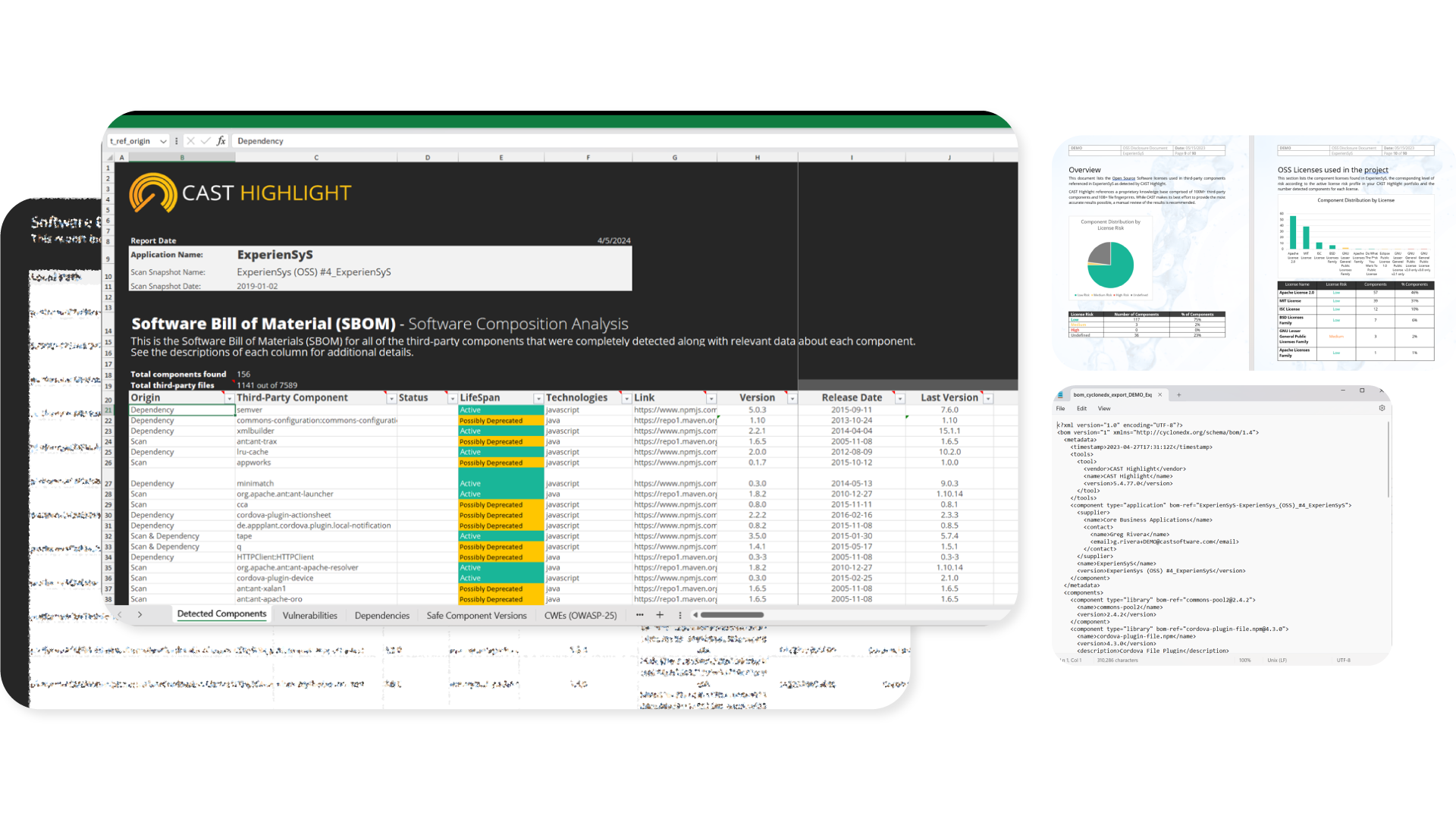
Download this sample SBOM file to learn what is included in a comprehensive SBOM such as:
- Inventory of all open source components
- Component details (version, release date, etc.)
- Security vulnerabilities (CVEs) and criticality
- Licenses and risk levels
- Possible licensing conflicts
- Transitive dependencies
- Software weaknesses (CWEs)
- Safer component version recommendations
Why do you need an SBOM?
Over 70% of applications utilize open source software (OSS) components to speed up development cycles, but this introduces legal, security, and obsolescence risks, according to Gartner. The ubiquitous use of OSS in the software supply chain has increased organizations' exposure to security attacks from hackers and legal action from IP owners. This has led organizations of all sizes globally to adopt a new standard for controlling open source risks requiring an SBOM to accompany any software being delivered, such as the recent cybersecurity executive order (EO) issued by the US federal government. Any business seeking to deliver software in today's environment needs the ability to produce an SBOM with speed and accuracy.
How do you automate SBOM creation?
CAST Highlight, a software intelligence product, plugs directly into source code repositories and analyzes applications in minutes, without disrupting developers. It performs Software Composition Analysis (SCA) of an application portfolio and automatically creates a full inventory of the 3rd party and Open Source components used within the codebase, including license versions. It highlights licensing exposures and security vulnerabilities as well as recommendations on the most critical remediations required. The SBOMs can be viewed and exported in Excel, Word, PPT, and CycloneDX.